Federated AAI Ideas
Degrees of Freedom
Type of Federation
Thank you David W. for mentioning the difference in the information publishing document.
Before taking any decision about the requirements for a federated AAI, one needs to be sure what type of federation is desired. There are roughly two types that need to be considered, which have a strong influence on how to authenticate and authorize users.
Tight federation
The federated cloud systems are all the same for the user. He only interacts with a single point of entry. Consequently, there can (and probably should) be a single user database.
Loose federation
Every user has a home organization at which he can be authenticated (identity provider). Every service within the federation 'knows' a list of acceptable identity providers.
VO support
Authentication -- What's already there?
Standards
SAML
" Security Assertion Markup Language (SAML) is an XML-based open standard for exchanging authentication and authorization data between security domains, that is, between an identity provider (a producer of assertions) and a service provider (a consumer of assertions)."
OAuth
"OAuth (Open Authorization) is an open standard for authorization. It allows users to share their private resources (e.g., photos, videos, contact lists) stored on one site with another site without having to hand out their credentials, typically username and password.
...
OAuth is a service that is complementary to, but distinct from, OpenID."
x.509 Certificates
incl. Proxies
Apache2 SSL reverse-proxy -- Configuration example
OpenID
OpenID is an open standard that describes how users can be authenticated in a decentralized manner, eliminating the need for services to provide their own ad hoc systems and allowing users to consolidate their digital identities. Users may create accounts with their preferred OpenID identity providers, and then use those accounts as the basis for signing on to any website which accepts OpenID authentication. The OpenID standard provides a framework for the communication that must take place between the identity provider and the OpenID acceptor (the ‘relying party’). An extension to the standard (the OpenID Attribute Exchange) facilitates the transfer of user attributes, such as name and gender, from the OpenID identity provider to the relying party (each relying party may request a different set of attributes, depending on its requirements).
AAI Products
Shibboleth
The Shibboleth System is a standards based, open source software package for web single sign-on across or within organizational boundaries. It allows sites to make informed authorization decisions for individual access of protected online resources in a privacy-preserving manner.
UVOS
UNICORE VO Service (UVOS) is a client-server system, developed to be used as an additional tool for large distributed systems. Grid systems, especially UNICORE grid middleware, are the mainspring of the UVOS system. Although UVOS can be used with different systems, however is designed primarly to support UNICORE grid middleware.
VOMS
VOMS is a system for managing authorization data within multi-institutional collaborations. VOMS provides a database of user roles and capabilities and a set of tools for accessing and manipulating the database and using the database contents to generate Grid credentials for users when needed.
A comparison of UVOS and VOMS can be found here:
- https://indico.cern.ch/contributionDisplay.py?contribId=8&sessionId=13&confId=124206
- https://twiki.cern.ch/twiki/bin/view/EMI/EmiJra1SecUVOSVOMSComp
VOMS support for OpenStack is available as a drop-in Python package. There is also some documentation about its configuration.
Cloud Product Support
One of the key factory influencing the choice of AAI will be the support in the already deployed Cloud products in the Testbed. Most likely, support will not be directly available. But where it is, it will be valuable. Most probably, we will have to evaluate the effort required to integrate AA support into the products.
OpenNebula
OpenNebula supports traditional groups - users are assigned to groups, access to various resources (hosts, virtual machines, templates, virtual networks) can be limited by group membership - based on group membership, user can see ony resources assigned to his group. Some resources can be owned only by one group (virtual machines, templates, virtual networks), some resources (hosts) are owned by system but access can be limited to list of groups and users.
OpenNebula also support ACLs, various operations with resources can be limited to specific user, example is described on , where subset of group users cab be defined as "administrators of resources".
OpenNebula has possibility to manage several instances of OpenNebule using one admin interface oZone , this feature can provides several features usually provided by VOs - based on oZones, groups, and ACLs several Virtual Data Centers can be created, resources can be assigned or dedicated to VDC, VDC has it's own manager, which can create users and manage resource assignment in such VDC=group etc.
OpenNebula has basic X.509 support, but no VOMS extensions are supported, so there is no mapping from VOMS attributes to groups or ACLs etc. (but seems to me that it could be implemented with reasonable effort).
OpenStack
Towards the end of 2010, OpenStack started their authn initiative to consolidate the various mechanisms available in the different components of OpenStack. The goal of this initiative was "to define a standard for authentication in OpenStack that enables services to support multiple authentication protocols in a pluggable manner".
Starting with its Diablo release, "Keystone is the identity service used by OpenStack for authentication (authN) and high-level authorization (authZ). It currently supports token-based authN and user-service authorization. It is scalable to include oAuth, SAML and openID in future versions."
Whereas in the Diablo release Keystone is an add-on component, the following Essex release provides Keystone as a core component.
Members of the Task Force have patched Keystone to support VOMS based VOs. See section #VOMS for further information.
StratusLab
The authentication uses the Jetty application server and the JAAS system to provide a wide variety of mechanisms for authenticating users. System administrators can choose to use:
- Username/password pairs maintained in a configuration file
- Username/password pairs from an LDAP server
- Grid certificates
- VOMS proxies created from grid certificates
WNoDeS
Infrastructure
EGI SSO
- What does it use?
- Possible integration?
Authorization
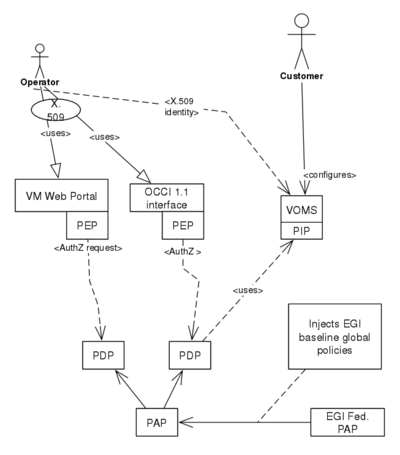
Authorization is the second principle by which users gain access to resources. In the same way as the authentication infrastructure (identity management), an authorization infrastrucuture must be put in place. Authentication and authorization infrastructure go hand in hand, as authenticated users must be mapped to appropriate policies. The authorization infrastructure is federated in the same way as the authentication infrastructure, although policies can be expected to be more hirarchical.
XACML
The predominant standard in terms of authorization is XACML. Products supporting this standard are:
- http://xacmlpdp.sourceforge.net/
- http://www.herasaf.org/
- http://sourceforge.net/projects/xacmllight/
- Others can be found at: http://www.oasis-open.org/committees/tc_home.php?wg_abbrev=xacml
The Argus product could be quite valuable in terms of liaisons with other projects. It supports XACML 2.0: