DCH-RP:PoC 2 Evaluate EUDAT services
| WP5: Proofs of Concept | Scenarios | PoC Phase 1 | PoC Phase 2 | DCH Glossary |
Introduction
This experiment will look at the suitability of the EUDAT services for DCH. The EUDAT project provides two services that may be of interest to the DCH community:
- B2SAFE - the central EUDAT service that offers functionality to replicate datasets across different data centres in a safe and efficient way while maintaining all information required to easily find and query information about the replica locations. The information about the replica locations and other important information is stored in PID records, each managed in separate administrative domains.The B2SAFE Service is implemented as an iRODS module providing a set of iRODS rules or policies to interface with the EPIC handle API and uses the iRODS middleware to replicate datasets from a source data (or community) centre to a destination data centre. See B2SAFE webpage for details.
- B2SHARE - (previously SimpleStore) is a customised version of Invenio (invenio-software.org) designed to offer a simple mechanism for uploading and sharing scientific data with associated metadata. It is intended for a large number of small files, like spread-sheet files with research data or analysis results, which may contain important data but do not easily fit in with regular data management. See B2SHARE webpage and B2SHARE User Documentation for details.
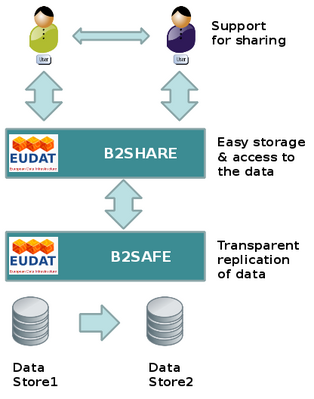
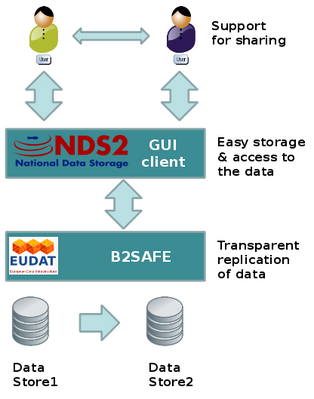
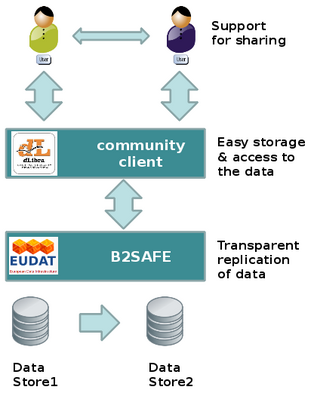
The B2SAFE service is interesting for DCH data from the point of view of assuring data sustainability and it will be used as a base layer for this experiment. However, B2SAFE offers quite low level interface which may occur impractical. The DCH institutions usually need easy access to their data and possibility to share the data between users and organizations. Thus, an additional layer for simplifying the access is needed. At the moment, three possible scenarios are considered, each of them using different tool or service as the upper layer of the software stack. They are shown on the below pictures:
B2SAFE workfow
The picture below shows B2SAFE workflow.