Difference between revisions of "Virtual Machine Image Endorsement"
| Line 69: | Line 69: | ||
== Securing services == | == Securing services == | ||
Follow the best practice guides for each service that's offered to the outside world. For instance, guides for [http://wiki.centos.org/HowTos/Network/SecuringSSH SSH] | Follow the best practice guides for each service that's offered to the outside world. For instance, guides for: | ||
*[http://wiki.centos.org/HowTos/Network/SecuringSSH SSH] | |||
*[https://www.owasp.org/index.php/Securing_tomcat Tomcat]. | |||
== Configuration == | == Configuration == | ||
Revision as of 07:42, 10 June 2015
Description
Goal
Set up a process assuring that a Virtual Machine Image (VMI)/ Virtual Appliance (VA) published in AppDB is well-configured, secure and up-to-date.
Members
- Enol Fernandez [EF]
- Vincenzo Spinoso [VS]
Contacts
SSO group available: vm-image-endorsement@mailman.egi.eu
Image types
| Type | Description | Managed by |
|---|---|---|
| EGI | General purpose images. Based on largely used Oses | EGI |
| VO-specific | VO specific images, available to a specific VO and customized for specific purposes | VO-expert |
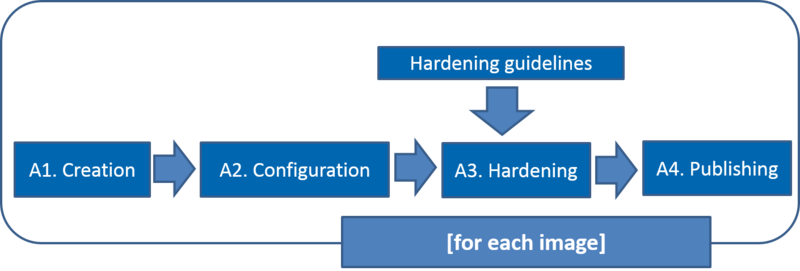
Activities and workflow
| Activity | Description |
|---|---|
| A1. Creation | Set up an image ready to be used by a Resource Provider |
| A2. Configuration | Configuration assures that packages are up to date and no wrong default configurations are left for any applications/services |
| A3. Hardening | Security is provided by applying CSIRT guidelines for the VMI Endorsement |
| A4. Publishing | Make image available on AppDB with proper tags, metadata, links |
Documents and Policies
Policies are defined by the SPG group and are published in the https://wiki.egi.eu/wiki/SPG:Documents
It is particularly relevant the Security Policy for the Endorsement and Operation of Virtual Machine Images and a draft of a Virtualisation Policy.
Hardening guidelines
Checklist kindly provided by David Groep.
Securing services
Follow the best practice guides for each service that's offered to the outside world. For instance, guides for:
Configuration
- remove all default passwords and accounts
- disable all services unless necessary for the intended tasks
- make sure the firewall config (iptables for Linux, also on IPv6) is minimally open
- put no shared credentials (passwords) in any image
Vulnerability assessment
Instantiate the image on a local network (without global connectivity) and run vulnerability assessment tools against it.
- from within the running VM image and quickly do some of the configuration checks is Lynis (working for most Unix/Linux flavours): which automates some of the testing of ssh/http/startup/etc configuration. Unpacking and running as root "./lynis --debug audit system" will give a wealth of hints and data. Many of these are hardening hints, so are not direct vulnerabilities, but merit review and warnings should be explainable.
- Run Nmap - it should show only intended open ports on the network. Try "sudo nmap -p- -sV -T5 192.168.0.103" and do that for both UDP and TCP. It should be rather quiet ... except for intended ports (a web site does need port 80 and 443 to be open).
- OpenVAS http://openvas.org/ install a machine on the same subnet and probe a running instance of the image
- Metasploit <http://www.metasploit.com/ have it try all possible exploits against your new VM from an adjancent machine
- if it's an RPM-package based system, run Pakiti http://pakiti.sourceforge.net/ against it. Debian currently does not provide approved data in CVE format.
Web applications
For web applications, run one or more of
- Nikto
- SQLmap to find SQL injection points
- Arachni finds XSS and XSRF exploits in web frameworks (works better when installed independently, not as part of OpenVAS).
Then explain notices on the false positives that are there.
Publishing
When publishing, each image will bring its own tags and metadata in AppDB (TBD).
Continuous improvement
It is important to understand how much each image is used. The "popularity" of a given image can be:
- most downloaded (AppDB)
- most used (accounting)
Procedures for EGI images
| Activity | Initial activity | Ongoing activity |
|---|---|---|
| A1. Creation | Set up the procedure for a given image | Use the procedure to create/update the image according to a given policy (on security issue, on request, every X days… ) |
| A2. Configuration | Create VMI configuration procedure for a given image | Apply VMI configuration procedure to a given image |
| A3. Hardening | Create VMI hardening procedure for a given image based on guidelines | Apply VMI hardening procedure to a given image |
| A4. Publishing | Publish the image on AppDB | Publish the image on AppDB |
Ubuntu
Creation
Configuration
Hardening
Publishing
CentOS7
Creation
Configuration
Hardening
Publishing
Procedures for VO images
The procedure is similar as to EGI images, but a VO expert (endorser) is fully responsible for the process of the endorsement of a specific VM. For the fedcloud.egi.eu VO the VO expert will get special help from EGI experts.